So finally, here it is…the part about Cisco's SDM. This beauty is used to help you configure a router from an HTTP or HTTPS interface. Actually, to be real, Cisco did produce something like this in the past, but honestly, it just didn't work all that well. This one does—really! And by the way, SDM is available on Cisco router models from Cisco 830 Series to 7301. Plus, it's preinstalled on all new 850, 870, 1800, 2800, and 3800 series routers. It's all good!
But there is a catch. Although the SDM is a really great tool, it's best if you pull it out just for advanced configurations—not the super-small, simple configurations like those we used in this chapter. Let me explain. Let's say you wanted to set up an advanced access list, VPN with IPSec, and intrusion protection on your router. If so, then SDM is your baby. You don't even have to know what IPSec means to configure it and make it work.
But again, there's both good news and bad news with this. Of course, we can now handle advanced configurations much more easily, but at the same time, it's not so good because, well, literally anyone can do the same thing!
What I'm going to do is show you how to log in using SDM; set your hostname, banner, and enable secret password; and assign a DHCP pool on a router and an IP address to an interface. And if it all goes well, after this section you'll find that SDM will turn out to be much more of a good thing because it will prove to be so much more helpful to you when you're reading the more advanced chapters on the IOS, NAT, wireless technologies, and security in both this book and the CCNA study guide than the way it used to be when we were all mired down in basic IOS router configuration. I'll use it a little in every chapter, both to show you the ease you'll gain and to explain its complexity. But I promise to truly expose the limitations of SDM as well.
Honestly, I could write a whole book about SDM, but I don't need to because Cisco did it already. To find more details about SDM, go to http://www.cisco.com/go/sdm. Plus, a new router will typically come with a CD that walks you through physically connecting your router and configuring it step-by-step (overkill in my opinion); you truly don't need this CD to connect to your router and use SDM.
All you need is a supported ISR router (1800/2800, etc.) and you can download the latest version of SDM complete with instructions for installing it on your computer and your router from the following location: http://www.cisco.com/pcgi-bin/tablebuild.pl/sdm.
| Note | To download this software, you need a Cisco Connection Online (CCO) login. However, this is free and only takes a minute or less to set up. Go to http://www.cisco.com and click on Register in the top-right corner. Fill in the short form, add the username and password you want to use, and you can now download the SDM and the SDM demo. |
From this site, you can not only install the SDM on your computer to help the SDM pages load faster when connecting to your router, you can also enable the use of the Cisco SDM demo itself.
| Note | I highly recommend downloading and running through the SDM demo if you don't have an ISR router to play with. First, install SDM on your computer, and then download the demo at http://www.cisco.com/pcgi-bin/tablebuild.pl/sdm-tool-demo. Read the install instructions, or run through Hands-on Lab 4.6 at the end of this chapter to get you set up and going strong with SDM. |
You need to know this though—to set up your host to log in using the SDM, you have to make sure your router is configured first. In the last CLI section of this chapter, I had deleted my configurations and reloaded the router, so I had to start from scratch. But doing that really isn't all that hard. You can just choose a LAN interface of the router and then connect a host directly to the router using a crossover cable—not so bad!
Would you like to enter the initial configuration dialog? [yes/no]: n
Press RETURN to get started!
Router>en
Router#config t
Enter configuration commands, one per line. End with CNTL/Z.
Router(config)#int f0/0
Router(config-if)#ip address 1.1.1.1 255.255.255.0
Router(config-if)#no shut
Router(config-if)#do ping 1.1.1.2
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to 1.1.1.2, timeout is 2 seconds:
!!!!!
Success rate is 100 percent (5/5), round-trip min/avg/max = 1/1/4 ms
So what's this all about? In the preceding configuration, I configured the FastEthernet interface with an IP address and enabled it with the no shutdown command. I then tested my connection by pinging my directly connected host from the router prompt. (This would be a minimum configuration and will allow you to connect via SDM.) From here, you just open a browser, with pop-ups enabled, type http://1.1.1.1, and follow the easy prompts once connected.
It's different if you want to set the router to use HTTPS, which allows you access into privileged mode upon connection (meaning we're setting the router back to the original default configuration). And you need to add a few more commands.
First, enable the HTTP/HTTPS server (your router won't support HTTPS if it doesn't have the advanced services IOS):
Router(config)#ip http server
Router(config)#ip http secure-server
% Generating 1024 bit RSA keys, keys will be non-exportable...[OK]
Router(config)#ip http authentication local
Second, create a user account using privilege level 15 (the highest level):
Router(config)#username cisco privilege ?
<0-15> User privilege level
Router(config)#username cisco privilege 15 password ?
0 Specifies an UNENCRYPTED password will follow
7 Specifies a HIDDEN password will follow
LINE The UNENCRYPTED (cleartext) user password
Router(config)#username cisco privilege 15 password 0 cisco
Last, configure the console, Telnet and SSH (if you want to use both Telnet and SSH) to provide local login authentication at privilege level access:
Router(config)#line console 0
Router(config-line)#login local
Router(config-line)#exit
Router(config)#line vty 0 ?
<1-1180> Last Line number
Router(config)#line vty 0 1180
Router(config-line)#privilege level 15
Router(config-line)#login local
Router(config-line)#transport input telnet ssh
Router(config-line)#^Z
Voilà! Now let's connect to my 2811 using HTTPS!
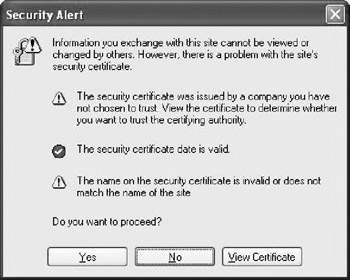
Okay—as soon as I connected via https://1.1.1.1, I received a security alert message.
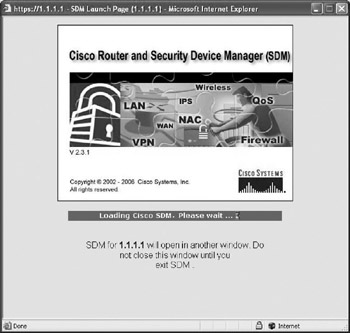
I was then prompted to log in with the username/password I created. SDM started loading and told me to hold on, which means it needs a bit of time to load another window. Do not close this window.
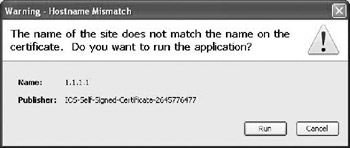
The certificate that I created with the ip http-secure-server command was loaded onto the router. I chose to click on Always Trust Content from this Publisher and then clicked Yes.
Of course, the certificate would not match any site name, so I then had to verify that I wanted to run it.
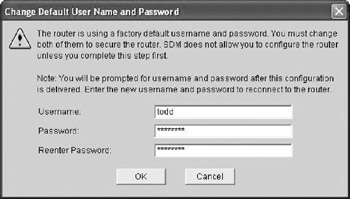
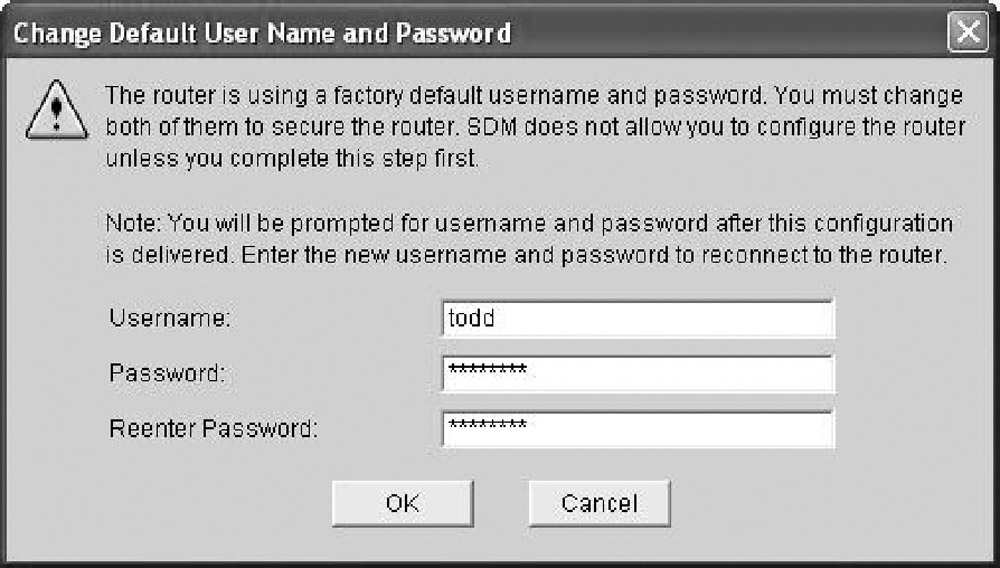
I then had to log in again and wait for SDM to load, during which time the router had me change my default username and password.
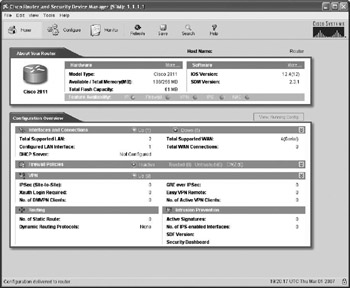
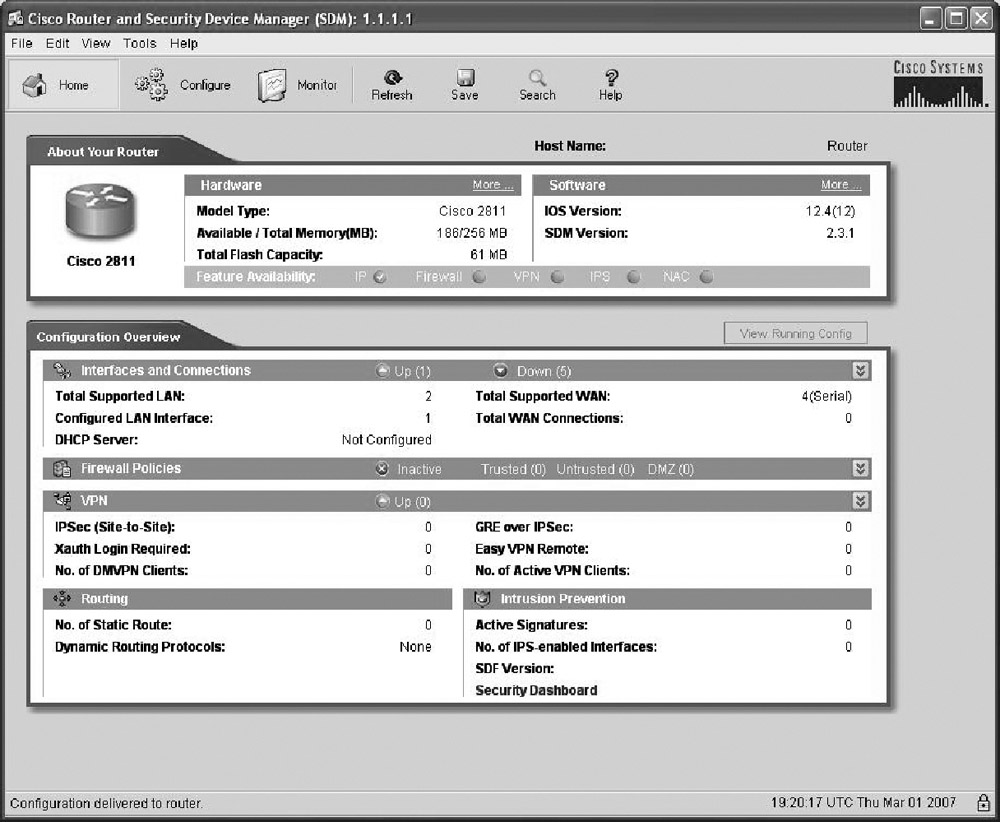
Finally—yes! I am connected to SDM!
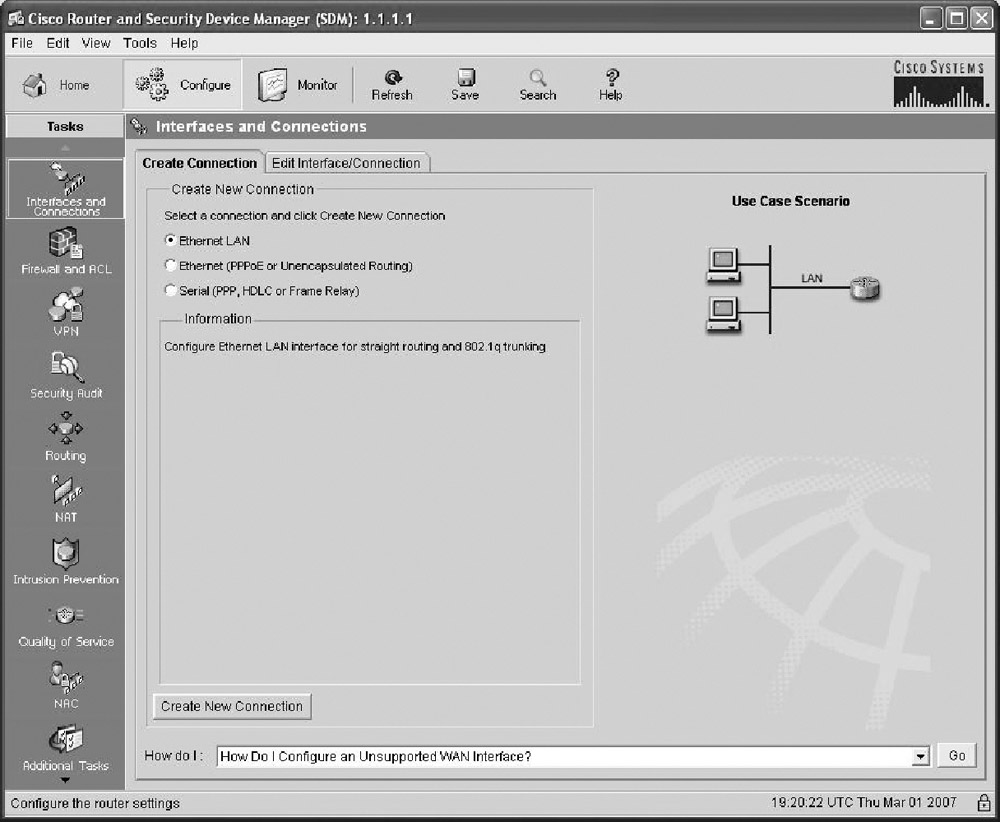
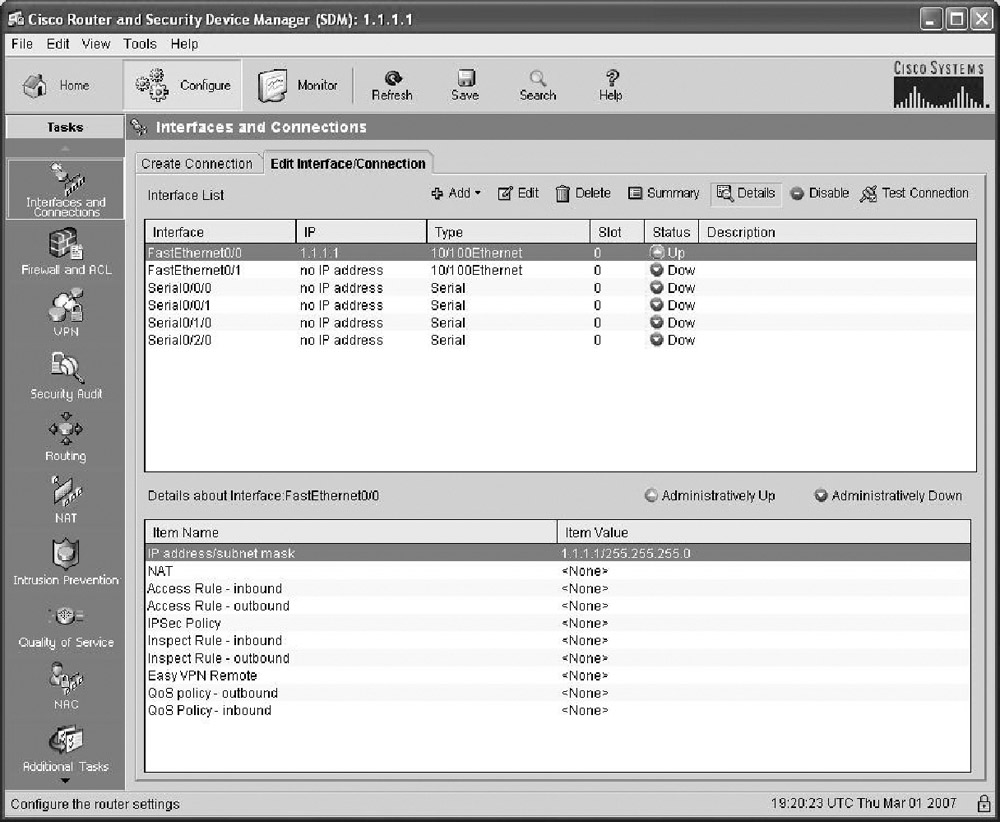
Clicking the Configure button at the top of the page, I chose to go step-by-step through interface configuration by first choosing the type of interface I wanted to configure and then clicking the Create New Connection button at the bottom of the page. This opens the LAN or WAN wizard, depending on which interface you choose to configure. (We'll configure our router interfaces with these wizards in Chapter 6.)
By clicking the Edit Interface/Connection tab, you get to see your interface status.
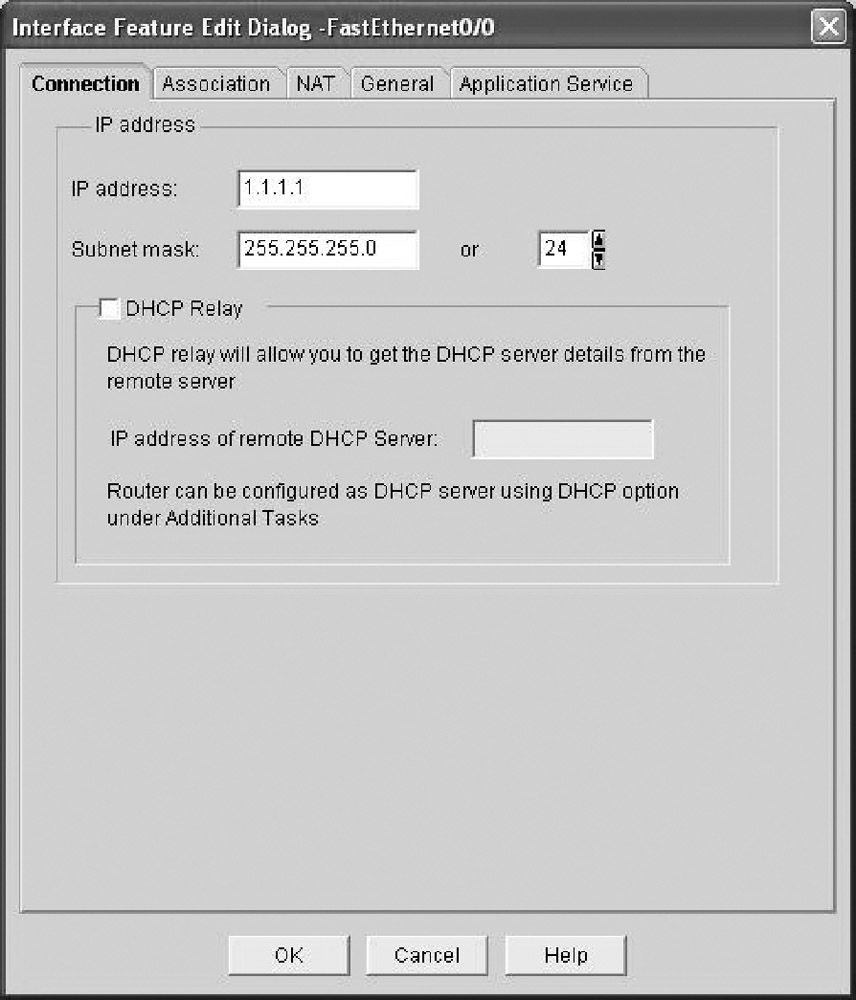
That's not all—just double-click on an interface to edit it. (You can only do this after you've gone through the LAN or WAN wizard and configured the interface.)
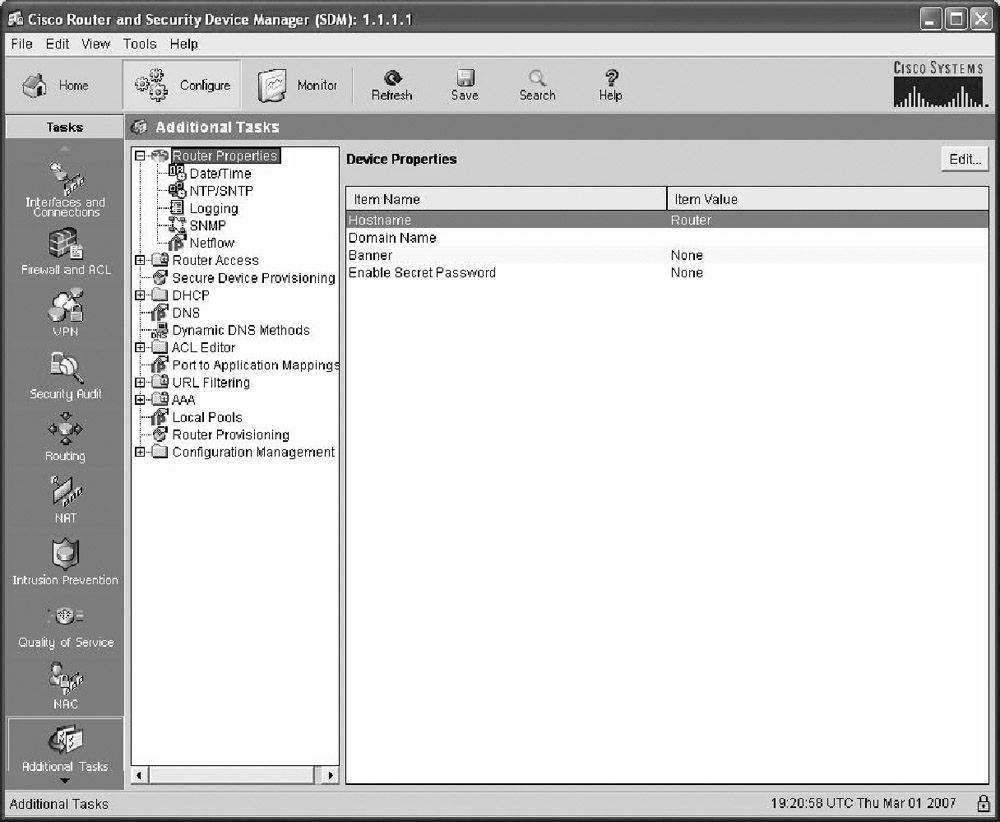
Look down at the bottom-left portion of the wizard page and click the Additional Tasks button. From there, just click the Router Properties icon.
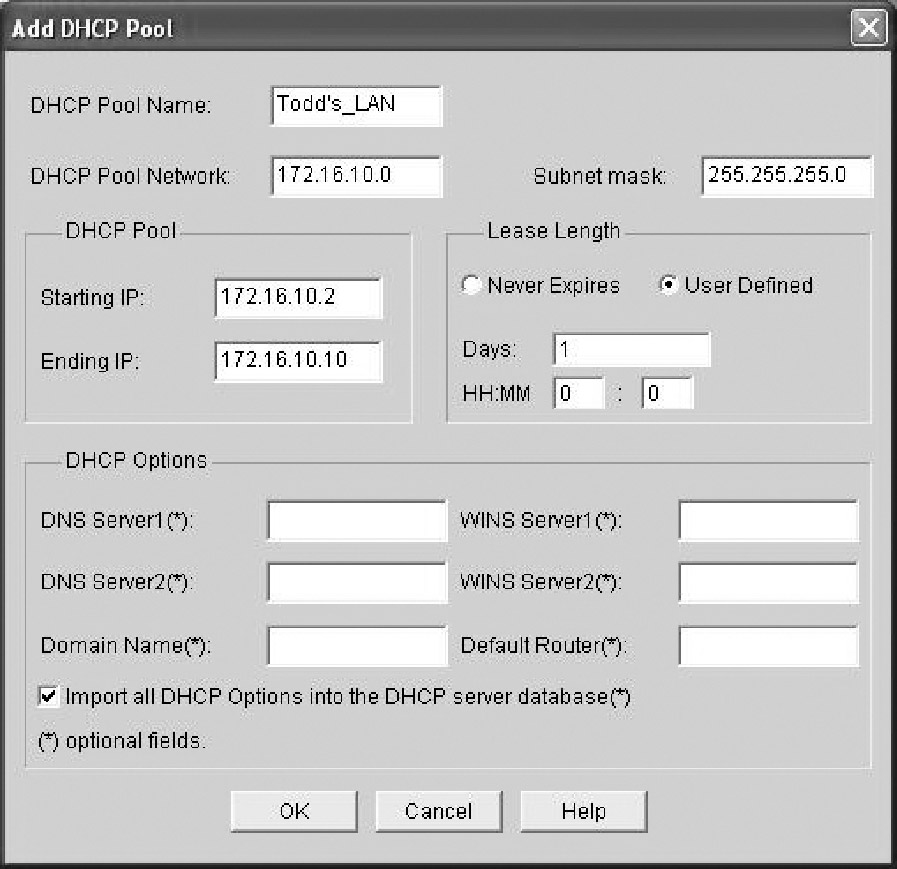
Here, you can set the hostname, MOTD banner, and enable secret password. Last, I clicked on the DHCP folder, then the DHCP pool icon. I then clicked Add and created a DHCP pool on my router.
Now, let's take a look at the configuration on the router:
Todd#sh run
Building configuration...
[output cut]
hostname Todd
!
ip domain name lammle.com
[output cut]
ip dhcp excluded-address 172.16.10.1
ip dhcp excluded-address 172.16.10.11 172.16.10.254
!
ip dhcp pool Todd's_LAN
import all
network 172.16.10.0 255.255.255.0
!
crypto pki trustpoint TP-self-signed-2645776477
enrollment selfsigned
subject-name cn=IOS-Self-Signed-Certificate-2645776477
revocation-check none
rsakeypair TP-self-signed-2645776477
!
crypto pki certificate chain TP-self-signed-2645776477
certificate self-signed 01
3082023E 308201A7 A0030201 02020101 300D0609 2A864886 F70D0101
04050030 31312F30 2D060355 04031326 494F532D 53656C66 2D536967
6E65642D 43657274 69666963 6174652D 32363435 37373634 3737301E
170D3037 30333031 3139313 33335A17 0D323030 31303130 30303030
305A3031 312F302D 06035504 03132649 4F532D53 656C662D 5369676E
65642D43 65727469 66696361 74652D32 36343537 37363437 3730819F
300D0609 2A864886 F70D0101 01050003 818D0030 81890281 8100BB24
[output cut]
quit
username todd privilege 15 secret 5 $1$nvgs$QRNCWKJ7rfmtNNkD2xvGq/
[output cut]
!
line con 0
login local
line aux 0
line vty 0 4
privilege level 15
login local
transport input telnet ssh
line vty 5 1180
privilege level 15
login local
transport input telnet ssh
!
So what we can see here is that the router created the hostname, DHCP pool, and certificate. We went through a lot of setup because we were using HTTPS—it's so much easier and unencumbered with less setup to just use HTTP. But remember, what we used was an ISR default configuration to connect using SDM. We'll continue to use SDM throughout this book, but I seriously encourage you to get SDM for yourself and start getting familiar with it!